What Is a Red Team Exercise? A Deep Dive into Offensive Security with AcaciaSec

In the ever-evolving cybersecurity landscape, traditional security assessments like vulnerability scans and penetration tests often fall short in simulating real-world cyberattacks. That’s where Red Team engagements come into play—an elite, comprehensive exercise that puts your organization’s defenses to the ultimate test.
At AcaciaSec, we specialize in offensive security operations that go far beyond checklists. Our Red Team services are designed to simulate sophisticated threat actors, revealing blind spots that conventional assessments may miss—before a real attacker exploits them.
What Is a Red Team Engagement?
A Red Team engagement is a full-scope, covert security assessment where ethical hackers mimic the tactics, techniques, and procedures (TTPs) of real adversaries. Unlike traditional pen testing, which is scoped and often isolated to certain systems, Red Teaming takes a holistic approach, targeting your people, processes, and technology in one coordinated attack simulation.
Red Team engagements typically include:
Social engineering (e.g., phishing, vishing)
- Physical security bypass
- Initial access via external attack vectors
- Lateral movement within the network
- Privilege escalation and data exfiltration
- Persistence and stealth techniques
The objective? To test your detection, response, and resilience to a real-world, stealthy adversary operating over days or weeks.
Why Red Teaming Matters
In today’s threat landscape, organizations face advanced persistent threats (APTs) that don’t announce their presence. They exploit human error, third-party weaknesses, and security gaps left unnoticed by compliance audits.
Red Teaming answers critical questions:
- Can attackers breach your perimeter?
- Are your detection and response teams prepared?
- Would you notice a stealthy lateral move or data exfiltration?
- How well do your security protocols hold up under real pressure?
How a Red Team Engagement Works at AcaciaSec
At AcaciaSec, we treat each Red Team engagement as a customized intelligence-driven operation. Our offensive experts, including specialists in biometric bypass, deepfake exploitation, and advanced evasion, craft unique attack paths based on your sector, threat profile, and digital footprint.
Our approach includes:
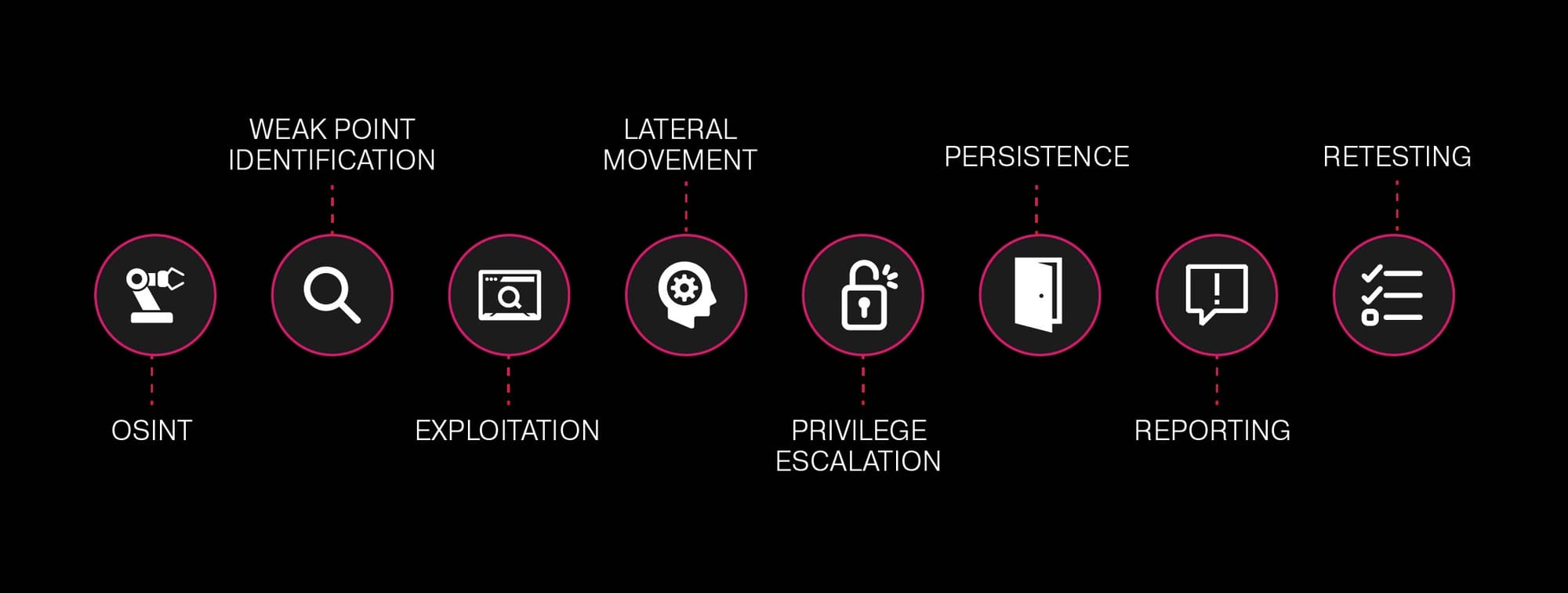
In 2025, attackers are leveraging AI-generated deepfakes, biometric spoofing, and emulated devices to bypass traditional controls. AcaciaSec has demonstrated—live—how these methods can be used to evade liveness detection in banking and identity systems.
If your security testing doesn’t include these next-gen threats, your organization is already falling behind.
🔒 Why Choose AcaciaSec?
Our team operates with the mindset of real-world adversaries, always staying one step ahead of the evolving threat landscape.
We are based in Florida, with operational presence across Latin America, and we’ve helped banks, governments, and critical infrastructure providers identify and close serious security gaps—long before they became news headlines.
Learn more about our Red Teaming services here, or contact us for a private threat consultation.
A Red Team engagement is your chance to uncover what a determined attacker could exploit before it’s too late. Are you ready to test your defenses?